SSRF Attacks via Webhooks: Protection Strategies
Learn how Server-Side Request Forgery (SSRF) attacks exploit webhook systems, discover real-world attack scenarios targeting cloud metadata and internal services, and implement proven protection strategies to secure your infrastructure.
SSRF Attacks via Webhooks: How to Protect Your Infrastructure
Server-Side Request Forgery (SSRF) attacks via webhooks are among the most dangerous vulnerabilities in web applications. SSRF ranks in the OWASP Top 10 and API Security Top 10, with attacks increasing 452% from 2023 to 2024 according to SonicWall research. Webhook endpoints remain a primary attack vector because they accept user-controlled URLs by design.
This guide covers how SSRF attacks work, why webhook systems are vulnerable, and concrete protection steps. See webhook security best practices for broader security guidance.
What is SSRF?
Server-Side Request Forgery (SSRF) is a vulnerability that allows attackers to induce your server to make HTTP requests to arbitrary destinations. Instead of attacking your application directly, the attacker weaponizes your server to attack other systems—often internal resources that would otherwise be inaccessible from the internet.
The attack flow:
- Attacker identifies an endpoint that accepts URLs as input
- Attacker submits a malicious URL pointing to an internal resource
- Your server fetches the URL, accessing the internal resource
- Sensitive data is returned to the attacker
Consequences: exposed cloud credentials, internal network mapping, data exfiltration, and full infrastructure compromise.
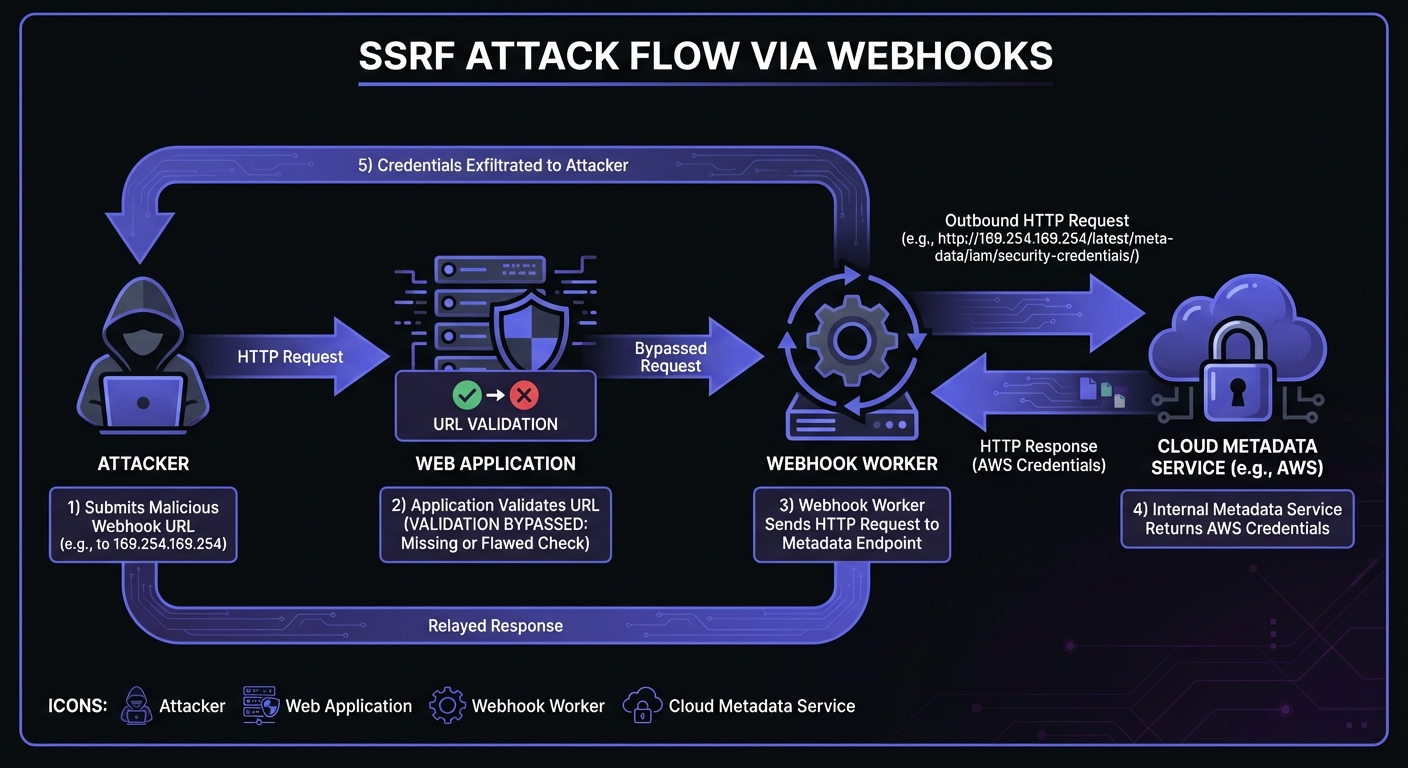
Why Webhooks Are Prime SSRF Targets
Webhook systems are inherently vulnerable to SSRF because they make HTTP requests to user-provided URLs. When an event occurs, your system sends data to whatever endpoint the user configured.
Without proper validation, an attacker can replace a legitimate URL:
// Legitimate
{
"event": "payment.completed",
"url": "https://customer-api.example.com/webhooks/payments"
}
// Malicious
{
"event": "payment.completed",
"url": "http://169.254.169.254/latest/meta-data/iam/security-credentials/"
}Your webhook delivery system sends a request to the malicious URL—the AWS metadata endpoint—potentially exposing IAM credentials.
Real-World Impact: The Capital One Breach
The 2019 Capital One breach demonstrates SSRF's devastating potential. An attacker exploited a misconfigured web application firewall on an EC2 instance, using SSRF to access the AWS metadata service at 169.254.169.254. The stolen IAM role credentials had excessive permissions, leading to exfiltration of over 100 million customers' sensitive data including Social Security numbers and bank account details. The 4-8 week recovery period and $80+ million in fines underscore why SSRF prevention is critical.
Real-World Attack Scenarios
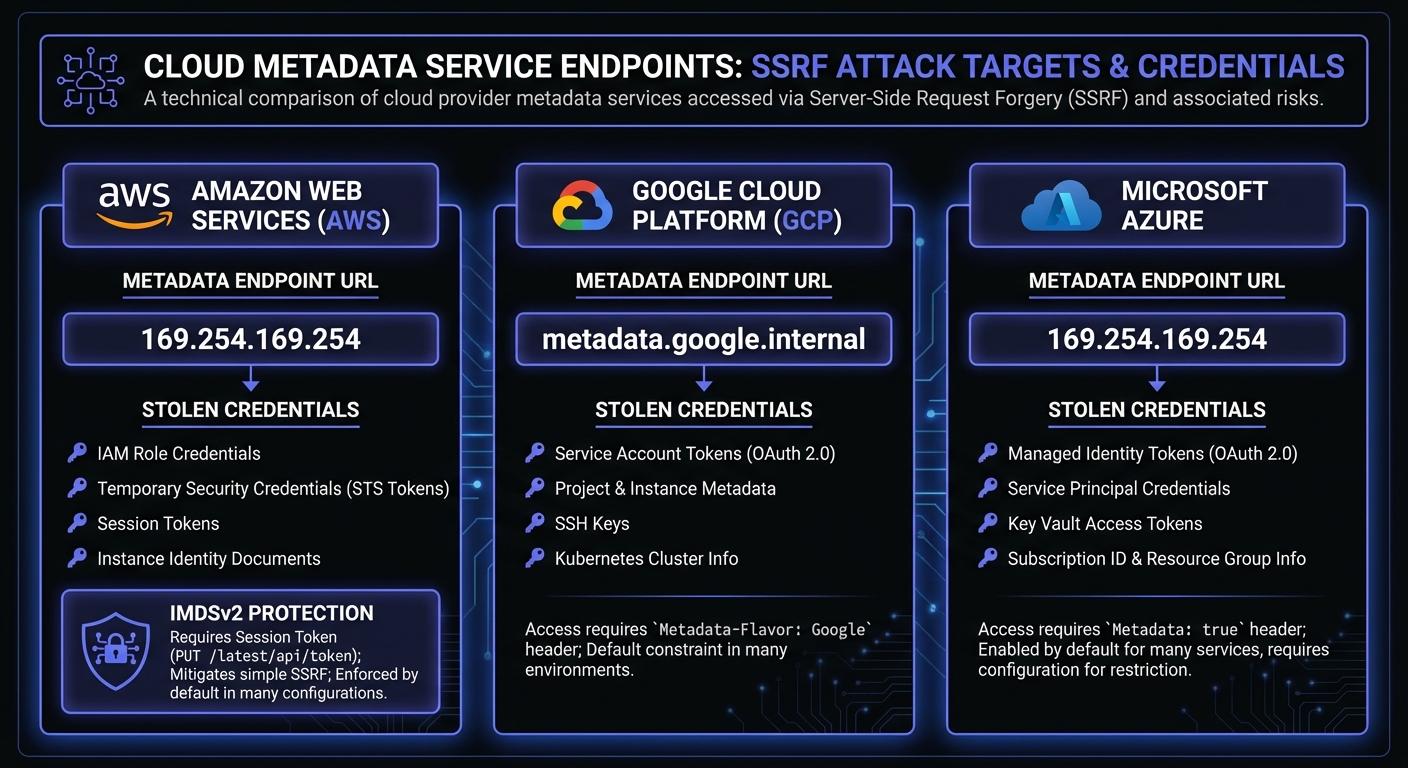
1. Cloud Metadata Endpoint Exploitation
Cloud providers expose instance metadata through well-known internal endpoints containing temporary security credentials, instance identity, and configuration data.
AWS Metadata Service:
http://169.254.169.254/latest/meta-data/
http://169.254.169.254/latest/meta-data/iam/security-credentials/[role-name]
Google Cloud:
http://metadata.google.internal/computeMetadata/v1/
http://169.254.169.254/computeMetadata/v1/instance/service-accounts/default/token
Azure:
http://169.254.169.254/metadata/instance
http://169.254.169.254/metadata/identity/oauth2/token
A successful attack yields temporary credentials with the instance role's permissions—potentially full access to S3 buckets, databases, and other AWS services.
2. Internal Network Reconnaissance
Attackers use SSRF to map your internal network by probing private IP ranges:
http://10.0.0.1:8080/
http://192.168.1.1/admin
http://172.16.0.50:3306/
By analyzing response times and error messages, attackers can identify live hosts, open ports, and running services. This reconnaissance enables targeted attacks against internal systems.
3. Internal Service Exploitation
Many internal services lack authentication because they're "protected" by the network perimeter. Common targets include:
- Redis/Memcached:
http://localhost:6379/ - Elasticsearch:
http://internal-es:9200/_cat/indices - Internal APIs:
http://billing-service.internal/api/invoices - Admin panels:
http://localhost:8080/admin
Once an attacker identifies these services, they can read sensitive data, modify configurations, or pivot to deeper network access.
4. DNS Rebinding Attacks
DNS rebinding bypasses URL validation by exploiting the time gap between URL validation and the actual HTTP request:
- Attacker controls a domain (e.g.,
malicious.attacker.com) - Initial DNS lookup returns a valid public IP (passes validation)
- DNS TTL is set very low
- When your server makes the request, DNS returns
127.0.0.1 - Your server connects to localhost, bypassing IP-based restrictions
5. Common Bypass Techniques to Guard Against
Attackers use creative techniques to circumvent naive blocklists:
Alternative IP representations for localhost:
- Decimal:
2130706433(equals 127.0.0.1) - Octal:
017700000001 - Shortened:
127.1 - IPv6:
::1,0:0:0:0:0:0:0:1
URL encoding and obfuscation:
http://127.0.0.1becomeshttp://%31%32%37%2e%30%2e%30%2e%31- Mixed case:
http://LocalHost/admin
Redirect chains: Attacker hosts a URL that passes validation, then redirects to http://169.254.169.254. Disable automatic redirect following or re-validate after each redirect.
Credential embedding: Using @ in URLs: http://expected.com@evil.com may resolve to evil.com on some parsers.
Protection Strategies
1. Strict URL Validation
Implement comprehensive URL validation before accepting webhook destinations:
from urllib.parse import urlparse
import ipaddress
import socket
BLOCKED_SCHEMES = {'file', 'ftp', 'gopher', 'data', 'javascript'}
ALLOWED_SCHEMES = {'http', 'https'}
def validate_webhook_url(url: str) -> bool:
"""Validate webhook URL for SSRF protection."""
try:
parsed = urlparse(url)
# Check scheme
if parsed.scheme not in ALLOWED_SCHEMES:
return False
# Require a hostname
if not parsed.hostname:
return False
# Block localhost variations
hostname_lower = parsed.hostname.lower()
blocked_hosts = {'localhost', '127.0.0.1', '0.0.0.0', '::1'}
if hostname_lower in blocked_hosts:
return False
# Resolve hostname and check IP
resolved_ip = socket.gethostbyname(parsed.hostname)
ip = ipaddress.ip_address(resolved_ip)
# Block private and reserved ranges
if ip.is_private or ip.is_loopback or ip.is_reserved:
return False
# Block link-local (metadata endpoints)
if ip.is_link_local:
return False
return True
except (ValueError, socket.gaierror):
return False2. Block Private IP Ranges
Maintain an explicit blocklist of private and special-use IP ranges:
BLOCKED_NETWORKS = [
# IPv4 ranges
ipaddress.ip_network('10.0.0.0/8'), # Private Class A
ipaddress.ip_network('172.16.0.0/12'), # Private Class B
ipaddress.ip_network('192.168.0.0/16'), # Private Class C
ipaddress.ip_network('127.0.0.0/8'), # Loopback
ipaddress.ip_network('169.254.0.0/16'), # Link-local (metadata!)
ipaddress.ip_network('0.0.0.0/8'), # Current network
ipaddress.ip_network('100.64.0.0/10'), # Carrier-grade NAT
ipaddress.ip_network('192.0.0.0/24'), # IETF Protocol Assignments
ipaddress.ip_network('192.0.2.0/24'), # TEST-NET-1
ipaddress.ip_network('198.51.100.0/24'), # TEST-NET-2
ipaddress.ip_network('203.0.113.0/24'), # TEST-NET-3
# IPv6 ranges
ipaddress.ip_network('::1/128'), # IPv6 loopback
ipaddress.ip_network('fc00::/7'), # IPv6 unique local
ipaddress.ip_network('fe80::/10'), # IPv6 link-local
ipaddress.ip_network('fd00:ec2::254/128'), # AWS IPv6 metadata
]
def is_blocked_ip(ip_str: str) -> bool:
"""Check if IP falls within blocked ranges."""
ip = ipaddress.ip_address(ip_str)
return any(ip in network for network in BLOCKED_NETWORKS)3. DNS Rebinding Prevention
Prevent DNS rebinding by resolving the hostname once and using the IP directly:
import requests
from requests.adapters import HTTPAdapter
class SSRFSafeAdapter(HTTPAdapter):
"""HTTP adapter that prevents DNS rebinding attacks."""
def __init__(self, resolved_ip, hostname, **kwargs):
self.resolved_ip = resolved_ip
self.hostname = hostname
super().__init__(**kwargs)
def send(self, request, **kwargs):
# Replace hostname with pre-resolved IP
connection_url = request.url.replace(
self.hostname,
self.resolved_ip
)
request.url = connection_url
# Preserve original Host header
request.headers['Host'] = self.hostname
return super().send(request, **kwargs)4. Network-Level Isolation
Defense in depth requires network-level controls:
- Dedicated webhook workers: Run webhook delivery from isolated instances with no access to internal networks
- Egress filtering: Configure firewalls to block outbound traffic to private IP ranges
- Separate VPC/network: Place webhook infrastructure in a network segment with no routes to internal resources
- Egress proxy: Route all webhook requests through a filtering proxy like Smokescreen that blocks internal IPs at the network layer
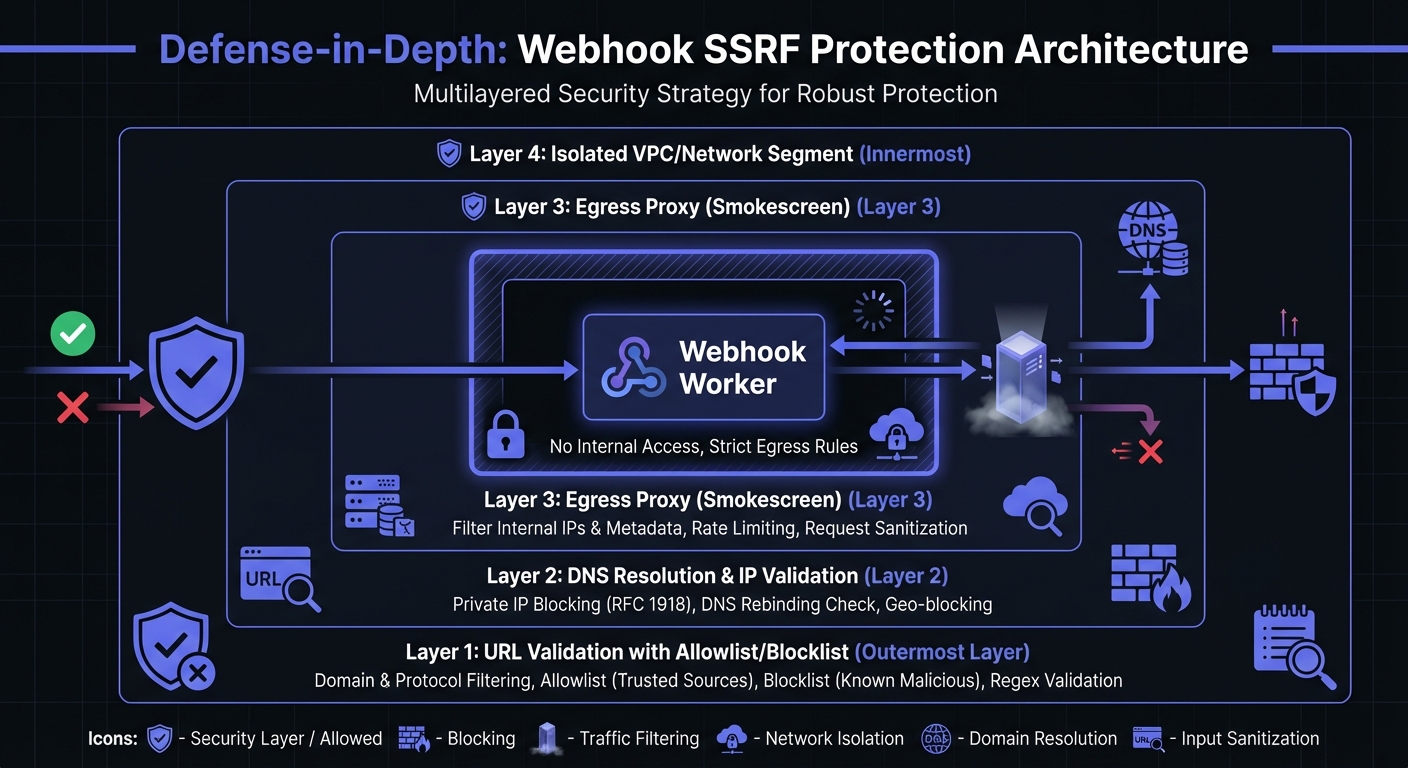
Combining IP validation with an egress proxy creates multiple protection layers. If a request bypasses initial validation through DNS rebinding or encoding tricks, the proxy blocks it before reaching internal resources.
5. Cloud-Specific Protections
AWS IMDSv2: Require token-based metadata access, which mitigates SSRF since attackers can't obtain the required token:
# Enforce IMDSv2 on EC2 instances
aws ec2 modify-instance-metadata-options \
--instance-id i-1234567890abcdef0 \
--http-tokens required \
--http-endpoint enabledGCP: Require the Metadata-Flavor: Google header, which most SSRF attacks can't set.
Azure: Use managed identities with minimal permissions and consider disabling metadata endpoint access where possible. Azure requires the Metadata: true header, providing some protection against basic SSRF.
6. Monitoring and Detection
Detect SSRF attempts before they succeed:
- Outbound traffic monitoring: Alert on requests to private IP ranges (RFC1918), link-local addresses (169.254.x.x), and cloud metadata endpoints from services that don't normally access them
- Redirect chain detection: Log and alert on suspicious redirect patterns, especially redirects from external to internal addresses
- Anomaly detection: Track baseline webhook destination patterns and flag unusual targets or sudden spikes in failed deliveries
- DNS query logging: Monitor for lookups resolving to private IPs from webhook workers
def log_ssrf_attempt(url: str, resolved_ip: str, reason: str):
"""Log potential SSRF attempts for security monitoring."""
logger.warning(
"SSRF attempt blocked",
extra={
"url": url,
"resolved_ip": resolved_ip,
"reason": reason,
"timestamp": datetime.utcnow().isoformat(),
"alert_type": "ssrf_attempt"
}
)
# Increment metrics for dashboard
metrics.increment("ssrf_blocked", tags={"reason": reason})Security Best Practices Checklist
Use this checklist to audit your webhook implementation. See our production webhook security checklist for comprehensive pre-production review:
- Validate URL scheme (allow only
httpandhttps) - Resolve hostnames before validation
- Block all private IP ranges (10.x, 172.16-31.x, 192.168.x)
- Block loopback addresses (127.x, ::1, IPv6 equivalents)
- Block link-local addresses (169.254.x, fe80::/10)
- Implement DNS rebinding protection
- Disable HTTP redirects or re-validate after redirects
- Set reasonable timeouts on outbound requests
- Log all webhook delivery attempts for monitoring
- Use network-level egress filtering
- Enable IMDSv2 on AWS instances
- Run webhook workers in isolated network segments
- Regularly audit and test SSRF protections
- Monitor for unusual webhook destination patterns
- Guard against bypass techniques (URL encoding, alternative IP formats)
- Use an egress proxy as secondary defense layer
How Hook Mesh Protects Against SSRF
Building robust SSRF protection is complex—many teams choose to build vs buy webhook infrastructure. Hook Mesh implements comprehensive safeguards:
Automatic URL Validation: Every webhook destination URL undergoes strict validation. We verify schemes, resolve hostnames, and block dangerous patterns.
Private IP Blocking: Automatically blocks requests to private IP ranges, loopback addresses, and cloud metadata endpoints.
DNS Rebinding Prevention: Resolves DNS once and pins the IP address, preventing time-of-check to time-of-use vulnerabilities.
Network Isolation: Delivery infrastructure runs in isolated network segments with no access to internal resources or metadata services.
Continuous Monitoring: Monitors delivery patterns for SSRF attempts and proactively blocks suspicious behavior.
With Hook Mesh, SSRF protection is built in. Focus on building your integration; we handle the security.
Conclusion
SSRF attacks via webhooks are serious threats. User-controlled URLs and server-side HTTP requests create an attack surface requiring careful protection. Implement strict URL validation, block private IP ranges, prevent DNS rebinding, and use network isolation to significantly reduce SSRF risk. Complete webhook security also requires proper authentication methods like HMAC signatures.
For startups without dedicated security teams, building these protections is complex. Managed webhook services like Hook Mesh handle these concerns out of the box, letting you focus on your core product. For more security guidance, explore our complete webhook security guide.
Related Posts
Webhook Security Best Practices: The Complete Guide
Learn how to secure your webhook implementations with HMAC signature verification, replay attack prevention, SSRF mitigation, and more. Includes code examples in Node.js and Python.
Securing Webhook Endpoints: A Checklist for Production
A comprehensive, actionable security checklist for production webhook endpoints. Covers transport security, authentication, input validation, rate limiting, logging, and error handling with priority levels and code examples.
Webhook Authentication: HMAC vs JWT vs mTLS Compared
A comprehensive comparison of webhook authentication methods including HMAC-SHA256, JWT, mTLS, Basic Auth, and API Keys. Learn when to use each method, with code examples and security recommendations.
Build vs Buy: Webhook Infrastructure Decision Guide
A practical guide for engineering teams deciding whether to build webhook delivery infrastructure from scratch or use a managed service. Covers engineering costs, timelines, and when each approach makes sense.